Marketplace Security Bug Bounty Program
A bug bounty program is one of the most powerful post-production tools to help detect vulnerabilities in applications and services.
The Marketplace Security Bug Bounty program is a collaboration between Atlassian and Marketplace Partners aiming to continuously improve the security posture of Atlassian Marketplace apps by leveraging crowdsourced vulnerability discovery methods available through bug bounty.
Apply to participate in this program. You'll need to have one or more publicly listed Marketplace apps in the Marketplace. Participation in the program is indicated on your Marketplace listing.
Program benefits and objectives
The program aims to give Marketplace Partners the tools to facilitate post-production vulnerability discovery in a cost-efficient way. If you are looking to start or extend your security story, the Marketplace Bug Bounty Program is a convenient way to ensure the security of your apps.
Flexibility
While Atlassian provides incentives and guidelines on how to run a successful bug bounty program, the details of implementation are largely determined by Marketplace Partners. This means that you can control the number of researchers invited to your program, the bounty payout structure, and the in-scope targets. Therefore, whether you want to begin security testing on all of your Marketplace apps, or with one or two and grow your program later, the Marketplace Bug Bounty Program can be tailored to fit your organization's requirements and use cases.
Customer trust
A bug bounty program helps increase trust between Marketplace Partners and customers. From the program, you can generate third-party penetration test reports for your customers. For reference, please see Atlassian’s published reports on the Security practices page. Bug bounty programs are also a useful addition to compliance and privacy programs.
Learn more about how customers evaluate trust in cloud.
How does the Marketplace Bug Bounty Program work?
The Marketplace Bug Bounty Program is hosted on Bugcrowd, a SaaS platform built to crowdsource vulnerability discovery from a global pool of talented security researchers.
The process is as follows:
-
Bugcrowd invites security researchers to participate in your private program.
-
When the researchers accept the invite, they're given instructions about what they are and aren’t allowed to test. For example, you may want the researchers to test your flagship Marketplace apps, but not your main website or your newer Marketplace apps. You also explain how to set up each of the targets, so they can start testing them quickly.
-
The researchers test your targets for vulnerabilities. If they believe they have detected a vulnerability, they report the finding using the Bugcrowd platform, and include enough detail for others to reproduce the vulnerability.
-
The Bugcrowd Application Security Engineering (ASE) reviews the report. They ensure the vulnerability is reproducible, is within the scope of your program, and includes any additional information you have requested.
-
When the ASE team is confident that the vulnerability report is valid, they flag it as triaged, and your team is notified that a potential vulnerability has been discovered.
-
Your team reviews the report to see if they agree with the security researcher and ASE’s assessment. If they agree that the vulnerability needs fixing, then you reward the security researcher with a bounty (see below for the recommended bounty amounts). This reward thanks the researcher and compensates them for their hard work and dedication in finding the vulnerability.
-
You create a ticket for your team to fix the vulnerability and improve the security of your application.
-
When the vulnerability is fixed, you notify the researcher and they are usually happy to test your fix.
And that’s it. Your application is more secure, the researcher moves on to look for more vulnerabilities, and the cycle begins again.
Resources to learn more
- Bugcrowd Welcome Center documentation
- What is Bug Bounty by Bugcrowd?
- Get started with your own Bug Bounty Program
- Getting value out of your Bug Bounty
Marketplace Bug Bounty Program requirements
We want to promote security-conscious apps in the Marketplace. When you participate in the paid bug bounty program, that participation is reflected on your Marketplace listing.
Requirements and how participation is shown are evaluated by hosting type. If your app has multiple hosting types (cloud and Data Center), each is evaluated independently and may have a different outcome.
Your app must meet the requirements below to be shown as participating in the Marketplace Bug Bounty Program.
Target naming scheme requirement
In order for our automation to properly identify your app, you must ensure that you define your targets according to the following standard format, which is adding the Marketplace listing URL in your target definition:
https://marketplace.atlassian.com/apps/<app_id>/<app_name>?hosting=<hosting_solution>
Your target definition on the Bugcrowd platform should look like this:
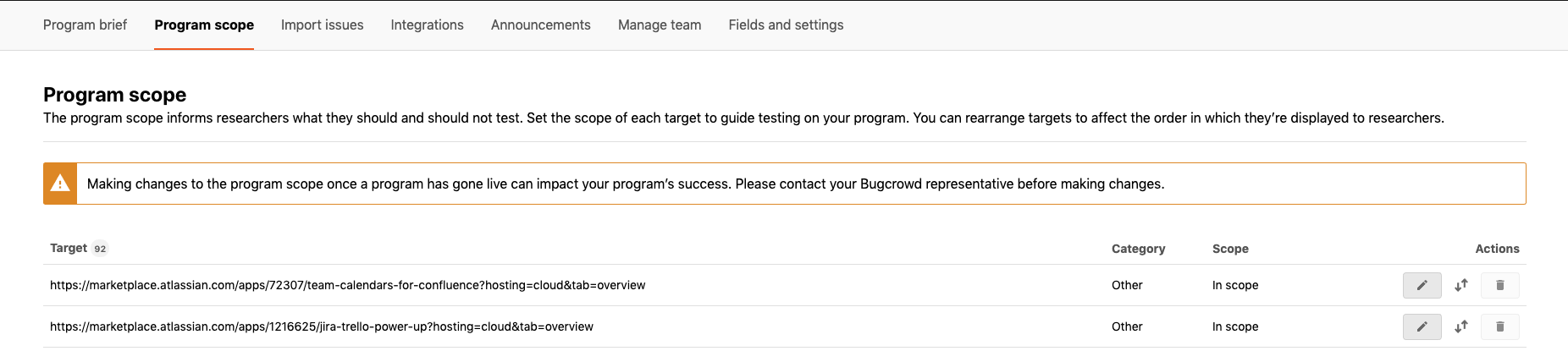
Make sure that each app in the target scope of your bounty program is the Marketplace listing URL and includes the hosting solution.
Other requirements
| Requirement | Description | Why is this important? |
|---|---|---|
| Participation | Eligible apps must participate in the Marketplace Bug Bounty Program. Participation means that an app is enrolled in the Marketplace Bug Bounty Program and is explicitly defined as a target in the program scope. Each hosting option of an app is considered a unique target. When an app is removed from program scope or when a program is paused, it will no longer meet the requirements to be shown as participating on the Marketplace listing. | This requirement ensures that you’ve authorized external researchers to test your apps for vulnerabilities, as well as committed to remediate security flaws in your apps. |
| Exposure | Eligible apps must be in scope of the Marketplace Bug Bounty Program for a minimum of 4 weeks and at least 100 security researchers must have been invited to the program. Note that time an app that participated in the Marketplace Bug Bounty Blitz counts toward this requirement. | This requirement ensures that your app has been exposed to security testing long enough for researchers to discover and report potential issues. |
| Incentives | Eligible apps must commit to the following minimum bounty payout structure: P1 → $1500 P2 → $900 P3 → $300 P4 → $100 | This requirement ensures that you give researchers proper incentives to participate in your program and focus on target apps. |
| Responsiveness | Eligible apps meet Triage SLAs for all incoming submissions. This means that reports must be accepted or rejected within 2 weeks after they have been triaged by Bugcrowd ASE | This requirement ensures that you review reports in a timely fashion and that there is a consistent feedback loop between you and security researchers. |
| Remediation | Eligible apps meet Remediation SLAs for all P1 (critical) and P2 (high) submissions. This means that critical and high severity vulnerabilities are remediated within Atlassian security SLAs. How to request SLA extensions for bug bounty submissions Whenever you receive a valid report through your bug bounty program, a corresponding ticket will be created in AMS. (To learn more about AMS and our approach to Vulnerability Management, please see this page). Please transition the ticket status to Extension Requested and provide an explanation for why the extension is needed in the ticket comments along with a remediation timeline. A member of Atlassian Security will review your request and either approve or deny it. If the extension request is approved, your app's participation status on the listing will be unaffected. Note that you are still responsible for meeting the new SLA to remain in good standing with program requirements. If the request is denied, your app may temporarily no longer appear as meeting program requirements on the listing until the vulnerability is remediated. | This requirement ensures that you are committed to fixing security vulnerabilities and that your remediation policy aligns with Atlassian standards. |
Additional recommendations
Atlassian has a long history of running a Bug Bounty Program. Through experience, we were able to narrow down a set of best practices that contribute to a successful program. We highly recommend for Marketplace Partners to consider these practices in addition to the program requirements listed above:
-
Assign a Bug Bounty program owner from your organization. The program owner is the point of contact for Atlassian should we need to get in touch about the bounty program.
-
Continuously assess the value the program provides. Ask yourself if you are getting the most value out of your program? If you’re not seeing a lot of submissions, consider adding new apps as targets, inviting more researchers to the program or increasing rewards.
-
Develop sound legal policy that protects both the company and the good-faith researcher. Policies like Safe Harbor allow organizations and researchers to set clear legal scope around parameters of testing.
-
Monitor and address program dormancy. Atlassian defines program dormancy as low researcher activity in a bug bounty program shown by few submissions, lack of reward payouts, or high false positive rate. While occasional low activity is normal, ongoing dormancy may require program changes as they may indicate larger issues in program setup. If you would like to tackle dormancy proactively, please raise an ECOHELP ticket here, for example by:
- Adding more researchers to your program
- Raising reward amounts
- Updating the brief and scope
Important: Atlassian may perform regular dormant program refreshes, contacting you by email to notify about dormancy and suggest actions to improve program performance. Ignoring the suggestions may result in your program being paused. Please whitelist this email address to avoid missing notifications: donotreply@atlassian.com.
-
Transition your program to public. All Marketplace bug bounty programs are required to transition to public. Public programs provide broader researcher access, more reliable reporting channels, and sustained program activity. Learn more about the requirements, benefits, and timelines of making your program public.
Automated program checks
In the first week of every month, Atlassian runs an automated check to verify that Marketplace Partners and their apps either continue to meet the Marketplace Bug Bounty Program requirements or newly meet those requirements.
Listing participation is updated based on the results. Occasionally the automation is delayed due to internal dependencies and may run a few days later than planned.
If you think your app's bug bounty participation status on the Marketplace is incorrect, please raise a request here.
Program cost
As part of the agreement with Bugcrowd, Atlassian covers all of the platform costs for our Marketplace Partners: you do not have to pay for access to the Bugcrowd platform and services.
You, as the Marketplace Partner, need to cover the costs of the bounty payouts. Below is a table of the minimum recommended payout structure for your bug bounty program.
| Vulnerability severity | Bug bounty reward amount (in USD) |
|---|---|
| P1 (Critical) | $1,500 |
| P2 (High) | $900 |
| P3 (Medium) | $300 |
| P4 (Low) | $100 |
| P5 (No appreciable security impact) | $0 |
Please note that you are not locked into the payout range you start out with. Instead, you can increase the payouts over time, as your program matures.
The decision about the severity of a vulnerability and the payout to the researcher is entirely at your discretion. You are not required to pay for duplicate submissions and will generally pay out only for the first report of any valid vulnerability.
Bug bounty reward pool
- Please note you will need to fund the bounty pool with Bugcrowd up front. This is to ensure there is an adequate reward pool for the initial submissions. It also ensures that submissions can be paid promptly, which encourages researchers to continue reviewing your app.
- You will be requested to fund a minimum of $5,000 USD to cover the program bounty pool.
- Additionally, you should expect to be adding to this fund as more findings are submitted, or your program may be paused until the pool is funded.
- If you do not spend the entire amount and choose to close out your program, the remaining amount will be transferred back to you.
How do I join the Marketplace Bug Bounty Program?
If you’re a Marketplace Partner in the Atlassian Marketplace, you can request to join the program by raising a ticket at this service desk. The Ecosystem Security Team will work with you to set up your program.
Please allow a minimum of 3 weeks from the date of your request to program launch.
Where can I get help with the Marketplace Bug Bounty Program?
If you’re a Marketplace Partner and you have been onboarded to Marketplace Bug Bounty Program, you can request to make changes to your program i.e. adding new target apps to program scope, inviting more researchers to your program or any other program support by raising a ticket at this service desk. The Bugcrowd Support Team will work with you to manage your program.
The Atlassian Ecosystem Security Team is also happy to answer any questions or queries you may have about the program via the same service desk. Alternatively, Bugcrowd offers a FAQ.
Rate this page: